If you run a business in an industry that transitioned to a remote-first or remote-optional model over the past year, you’ve probably had to adjust more than your videoconference camera. While your employees figured out how to stay productive while chaos swirled around them at home and around the world, you had to rethink how your company uses technology—including how to keep it secure without as much centralized control.
If you pay attention to the news, you’re aware that cyber crime is spiking during the COVID-19 pandemic, fueled by bad actors keen to take advantage of a vulnerable population of remote workers. But you don’t have to fall victim to cyber threats, even in a work-from-home world. The key to protecting your business from digital harm is to create (and enforce) a strong cybersecurity policy.
Why Do You Need a Cybersecurity Policy?
A cybersecurity policy sets the requirements and expectations for how your company will address specific issues related to protecting your digital environment and information assets. In reality, you will likely need a set of multiple cybersecurity policies to cover a broad spectrum of activities such as data backups, multi-factor authentication, endpoint protection, and more.
While it may take considerable time and effort to shore up every area of your company’s digital environment, there are some crucial steps you can take right away to start protecting your business. Here are the top five cybersecurity policies that should be part of all cyber risk management strategies:
- Multi-factor authentication: These systems (also referred to as MFA or two-factor authentication / 2FA) usually require a password plus another form of authentication such as a code or number from a key fob, a chip from an ID tag, a biometric reader of some type, or a code sent to a phone and typed in after the password. Requiring multi-factor authentication significantly reduces the likelihood that a hacker will be able to enter your systems through a credentialed access point.
- Encryption at rest: When data is stored in a long-term static state (think: all the drives where data can remain inactive—hard drive, thumb drive, cloud drive, etc.), it is known as at rest. Even when data is at rest, it needs to be encrypted so hackers can’t read it even if they infiltrate your systems and gain access to it.
- Encryption in transit: When data is shared over a network or stored in memory, it is considered in transit. It is equally important to encrypt data in transit so that hackers attempting to intercept data that is actively being processed can’t use the data even if they succeed in accessing it.
- Data backup and recovery testing: Most people know by now that they should make copies (also known as backups) of their data to store in a secondary location in the event of data theft, loss, ransomware, etc. But the key to this critical policy is the recovery portion. Having a second set of data won’t help you if you don’t have a way of restoring lost data through an established recovery process. Make a data recovery plan and test it often.
- Security awareness training with phishing simulation: People are one of a company’s greatest assets, but they can also be one of its largest liabilities, especially when it comes to cyber risk. Conduct ongoing training with employees and other stakeholders to help them improve their knowledge of good cyber hygiene practices. Be sure your training program includes some form of phishing simulation so your people can help protect the company from this increasingly common and sophisticated type of cyber attack.
How to Develop a Cybersecurity Policy
Developing a cybersecurity policy from scratch can be challenging, but there are many good resources and experts available to help if you don’t know where to start. When considering how you want to build your policy, there are several important components:
- Vulnerability and risk assessment: In-depth technical scans can highlight where your systems are most vulnerable, and a cyber risk assessment will evaluate the state of your existing risk management programs.
- Risk register: A risk register lists and details the various types of cyber risks your business is facing. It should also estimate the probabilities of risks negatively impacting your business, as well as provide recommendations for how to mitigate risks to reduce their potential harm.
- Controls and procedures: Security controls help you reduce or eliminate identified risks by prescribing the necessary activities and procedures needed to protect your data and systems.
- Implementation and management: Once you have outlined your policy, you need to assign someone to oversee the policy’s implementation and ongoing management. Without proper maintenance and enforcement, a cybersecurity policy won’t keep your information safe. It must be acted upon in real life in order to be effective.
Compliance with Cybersecurity Policies and Frameworks
There are several frameworks available to help inform your security policy development. Some of the most common guidelines include:
- SOC2
- ISO 27001
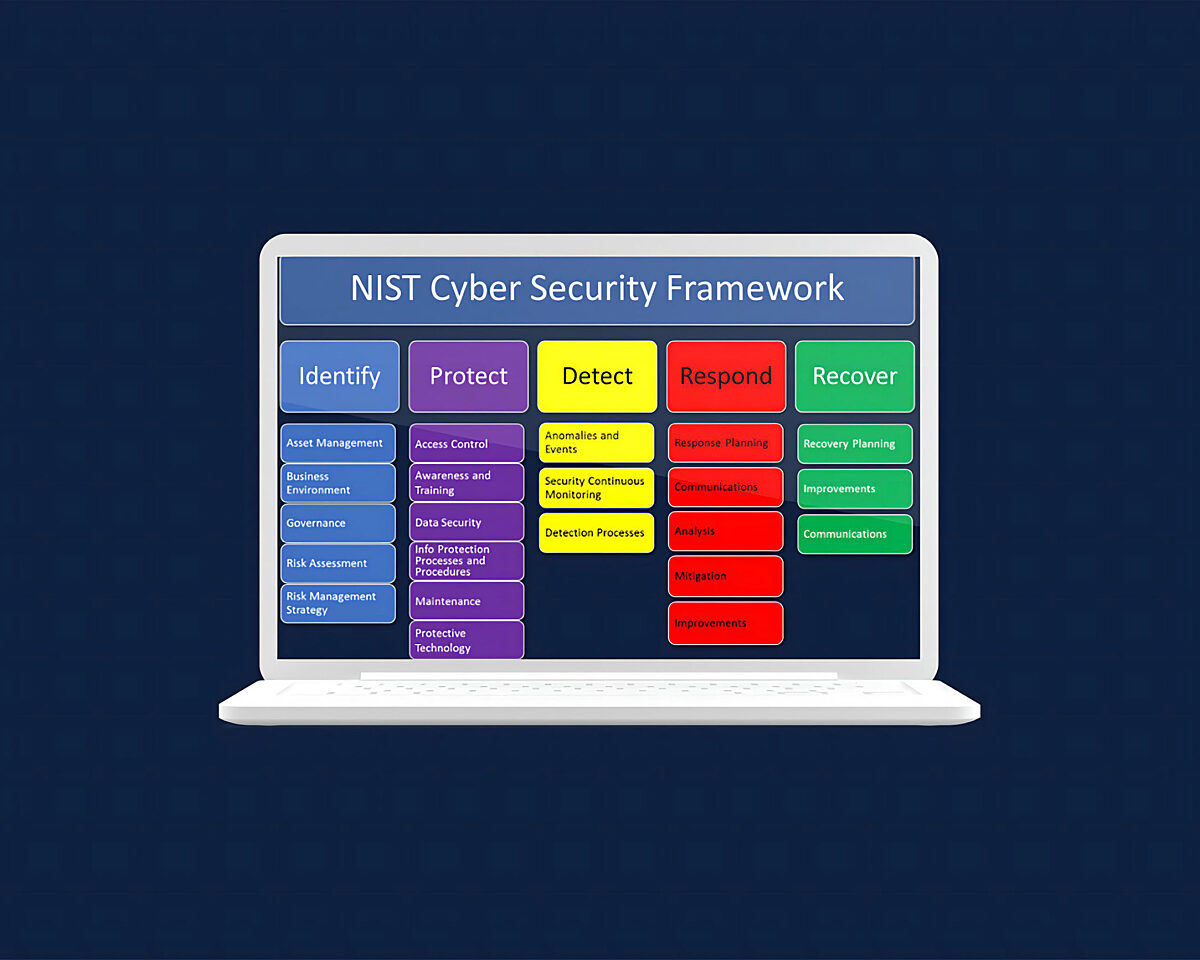
- NIST CSF
- DFARS
- CMMC
- NIST 800-171
- GDPR (and related privacy frameworks)
If you’re looking to achieve compliance with one or more of the above frameworks, you may want to consult an expert who can help you prepare for an audit and certification. Trava offers compliance-as-a-service to help customers manage their cybersecurity policies, risk management programs, and framework certification processes. If you’re ready to hand off the compliance hassle to the pros, let’s talk.