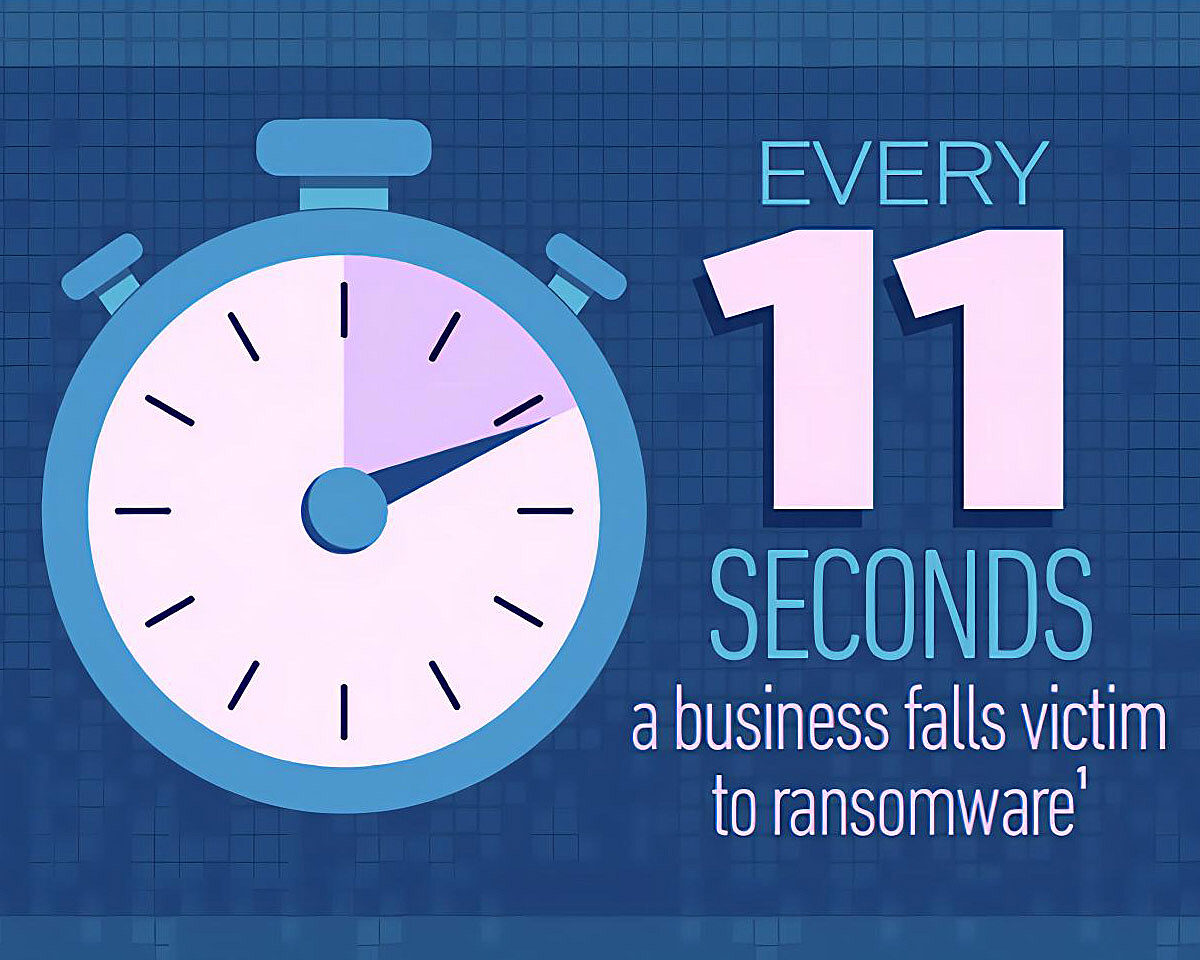
Every 11 seconds. That’s how often a business falls victim to ransomware.[1] And that’s how we introduced Part 1 of this blog series that examined the first five of the 10 most important things you as a business leader can do to protect your data and your clients’ data. In Part 2 of this series, we explore the next five.
6. Ensure successful configuration management
Configuration management is the process of identifying, controlling, accounting for, and auditing changes made to a pre-established baseline. Configuration management will control changes and test documentation throughout the operational life cycle of each technology component and software title. When it comes to mitigating risk, it provides visibility and tracking of changes to your system. If an actual event does occur, configuration management is essential for disaster recovery.
But what if?
Our goal at Trava is to help small and medium-sized businesses reduce the risk of cyber threats with our comprehensive cyber risk management solution. But what if an incident or a breach happens anyway? Unfortunately, no system is ever 100% secure. The good news is that if you have taken the first six steps outlined in this blog series, your recovery will be more manageable. And there’s more you can do.
7. Plan for an event
Prepare a disaster recovery plan and update it regularly. Make sure to include communications templates so that you can notify your clients and other key stakeholders immediately without having to spend time crafting the message at the time of the incident.
Have a disaster recovery team in place that is actively engaged in reviewing and updating the plan (refer back to Step 6).