Now more than ever, it is crucial for businesses to take care of their online presence. After all, the majority of consumers will be using the internet when looking for the next products and services they plan to purchase. Therefore, if you intend to generate more business, then you need to focus on your digital presence. For B2C (business-to-consumer) businesses it is a good idea to offer your products online through an e-commerce site.
There’s a flip side, too: Having a strong digital presence can also lead to serious vulnerability issues. As a result, every business needs to take the appropriate precautions to protect itself. If you are looking for a way to protect your business online, then you also need to think carefully about what kind of risks you have. The best way to figure this out is to use vulnerability assessment tools.
If you are looking at options for vulnerability assessment tools, you want the right vulnerability management tools for your business. As you continue to review a list of vulnerability assessment tools, you need to consider what common vulnerabilities your business might have to account for. For example, one of the biggest risks for today’s businesses, from small to enterprise, is called ransomware. Ransomware is a serious issue because it can take your files, encrypt them, and make everything in your business unusable until you take the action the hacker is demanding. In the worst cases, anything that has been connected to the internet could become frozen. Therefore, you need to make sure that you protect your business and its digital assets against this particular kind of risk.
This is only one of the many risks that you need to be thinking about. There are also plenty of other business vulnerabilities that you have to consider. But if you think carefully about the risks at hand, then you can take the right steps to protect your company.
This is all time consuming and might be overwhelming. As a business leader you already have a lot on your plate. Because of this, you may not have the free time to be thinking about the security of your business 24/7, especially when circumstances and best practices change so quickly. The right vulnerability tools can work wonders here, and as a result, you should look into which tools will be the best fit for your business.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Free Vulnerability Assessment Tools
If you are new to this area, then you may not know exactly what type of tools you are looking for. If that is the case, you are certainly not alone. A good way to get started is to consider free vulnerability assessment tools. There are plenty of vulnerability scanning tools that offer free options. If you use a vulnerability scanner free download, then you will be able to figure out what features you need, what features you do not, and what sets some tools apart from others.
At the same time, keep in mind that a free tool will only get you so far. Eventually, you will want complete visibility of everything that has to do with your company in the digital world, and free tools are limited options that just can’t provide this. Instead, the only way you will be able to enjoy this is if you are willing to invest in your cybersecurity options, which include premium vulnerability assessment tools.
Because of this, you’ll need to be willing to identify and invest in the right type of system for your company, even if this does require you to spend some money doing so. Of course, it still makes sense that you also want to keep your overhead expenses as low as possible. However, incurring some costs for finding the right system to help you now can lead to considerable savings in the future, when your business’ vulnerabilities have been protected against attacks that might otherwise damage your entire company. Because of this, it might be a good idea to reach out to cybersecurity professionals who can help you find the right tools for your company and its needs.
Database Vulnerability Assessment Tools
Your business has a lot of important assets, and one of the most important is its data. No matter what industry you operate in, there is probably a lot of important data that your company collects. For example, you may have a lot of personal information on your clients, including their names, addresses, and phone numbers. You probably also have the same information from your employees. In addition, if you have an e-commerce site, your company probably stores a lot of important payment information from your customers, including bank account information, credit card numbers, and debit card numbers. Therefore, you need to make sure that you protect this kind of data from cyber criminals who may want to steal it. This is where database vulnerability assessment tools can be vital. They can show you where cyber criminals might have an in.
There are numerous database auditing tools that you can use to do this. For example, you may want to use a free database vulnerability scanner. However, even though a free tool can certainly help you get started, you need to invest in your database security eventually in order to get the full range of protection available. This is where it is often helpful to use a vulnerability assessment questionnaire. By taking a closer look at a security vulnerability assessment example, you can figure out which of the tools or methods used will help you protect the integrity of your database. If you can protect your data from being stolen by hackers, you can instill a measure of confidence in your clients.
Vulnerability Assessment Methods and Tools
It is important for you to take a closer look at a vulnerability assessment methodology so that you understand the most important vulnerability assessment methodology factors that will play a role in protecting your company from harm. When taking a closer look at vulnerability assessment methods and tools, for instance, it is often helpful to take a look at a vulnerability assessment methodology example in the form of a PPT that you might find in an online search.
One of the most important tools you can use to protect your data from being stolen is called two-factor authentication. If you take advantage of vulnerability assessment methodology two factors, this is one of the more common means of protecting your business from data theft. The idea behind two-factor authentication is that if someone steals the password to one of your databases or other applications, they will not have the other factor they need in order to get in. For example, when someone uses their username and password to log into an application, the website might automatically send a text message to the number on file, asking that person to click the link before access will be granted. In this way, any unauthorized persons might have obtained the password, but they won’t have the second factor—that authorized user’s phone number—that would let them log in all the way.
This is just one of the many ways in which businesses can protect themselves from harm. Another important strategy that businesses should follow is to re-evaluate their security measures regularly. This is because, just as security technology has come a long way, hackers are also innovating and working hard to keep up as well. Therefore, all companies need to regularly re-evaluate where they stand when it comes to website security. If businesses take a look at their digital security on a regular basis, then they have a better chance of staying one step ahead of cybercriminals. This is a great way for companies to protect their information from being stolen.
Some businesses may believe they do not have time to re-evaluate cybersecurity regularly, not realizing what the consequences can be if they don’t. This is yet another reason why they need to put advanced tools to work for them. By automating the process, it is possible to save time and money without sacrificing the quality of cybersecurity.
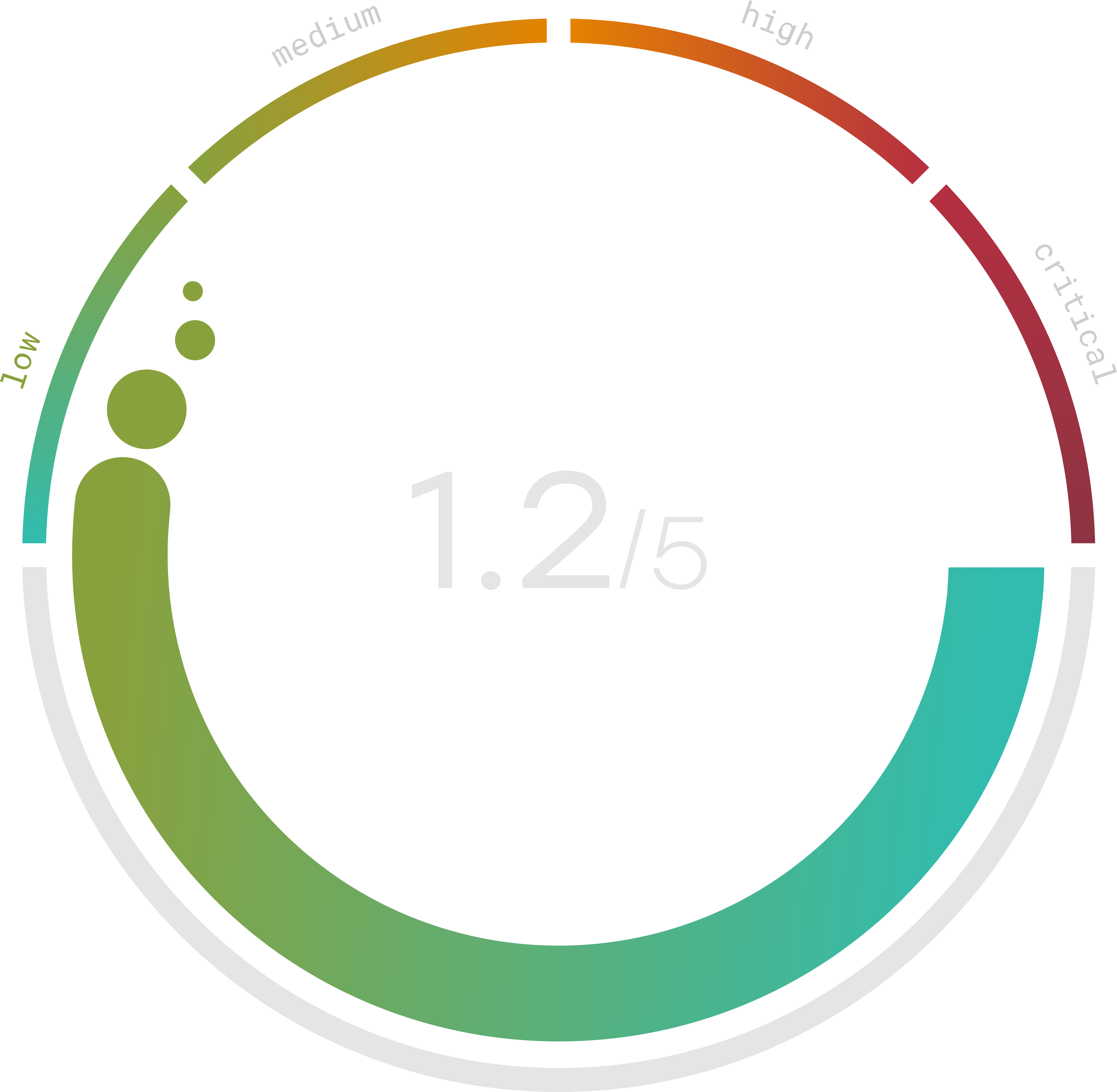
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Vulnerability Scanning Tools Comparison
Clearly, there is a lot to think about when it comes to vulnerability assessment tools. For instance, when looking at a vulnerability scanner online, businesses may be looking for a vulnerability scanning tools comparison. There are several options available, including:
- Some businesses may like to use the Qualys vulnerability scanner. This is a tool that has been around a while and has a strong track record. At the same time, it may not be able to protect against the most recent threats.
- Other people might be looking at the Acunetix vulnerability scanner. This is a cost-effective tool that can be used to help businesses guard against certain threats. On the other hand, this may not be the most reliable program.
- There are a lot of businesses that also prefer the Nexus vulnerability scanner. Even though this scanner is easy to use, it does not detect everything. The holes in this scanner mean that it isn’t the strongest vulnerability assessment tool available.
Clearly, there is a lot to consider when businesses are looking for the best vulnerability scanner 2021. In addition to the items named above, some people may like the Scuba database vulnerability scanner while others prefer the Nessus vulnerability scanner features.
Anyone looking for the best vulnerability scanner this year should also take a closer look at Travasecurity.com. This is currently the top option available for cyber risk management. Its features include an inexpensive price tag, ease of use, regular updates, and the ability to protect a business against the biggest threats out there. Therefore, businesses that want to make sure they cover all potential vulnerabilities and holes in their digital security coverage should consider taking advantage of this tool.
Website Vulnerability Scanner
In the end, businesses need to think carefully about protecting their online presence and assets. It is critical to use a website vulnerability scanner for this; however, it is also important to take a closer look at a vulnerability assessment chart, such as on a PDF, to see what it covers. By doing this, businesses can find the best web vulnerability scanner to meet their specific needs. Keep in mind too, that there are plenty of open source vulnerability scanning tools; however, the code for these tools can be edited by just about anyone, so they are not necessarily reliable.
Remember that there are many people who might be wondering whether “vulnerabilities are determined by which two factors,” which are evaluation and penetration testing. As these two factors reveal, you need to evaluate the quality of your cybersecurity regularly. One of the main ways you can do this is by running penetration testing. This is an important feature that you will need to find in whatever website vulnerability scanner you decide to use.
After all of this, you may be wondering which website vulnerability scanner is best for you. Fortunately, this is not necessarily something that you have to handle on your own. If you have questions about which website vulnerability scanner or other vulnerability assessment tools will be best for your company, do not hesitate to reach out to trained cybersecurity professionals who can help you make the most informed decisions. If you reach out to professionals who can help you find the best vulnerability scanner, then you can also reduce the chances of your website or data being stolen or hacked.
