SOC2 Compliance Checklist
When it comes to personal information, potential clients prefer some level of trust with the companies they choose to hold that information of theirs. A SOC2 attestation certification is a great way to show your patrons that you are doing everything necessary to comply with the SOC2 standards. So, is SOC2 worth it? Absolutely.
Platforms and services like Bytchek and Trava often offer a sort of SOC2 compliance checklist to make sure your security is up to par and ready for a security audit. These are essentially presented as a type of SOC2 questionnaire that is designed to evaluate your level of compliance and pinpoint trouble spots you need to work on to pass your security audit. There are free SOC2 audit checklist PDF downloads available online, but without experts in your corner, there is only so much these can do.
SOC2 attestation compliance is more than just a badge of honor to show your clients. It is a respected certification because of the areas of your security it involves. Data is a core aspect of many businesses these days. Especially with many companies switching to digital and online office spaces to adapt to the pandemic in 2020. SOC2 functions off of the five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
It is voluntary, but as stated above, it is one of the more respected ways a service company can prove their dedication to data security. A SOC2 certification means your company puts client data at the top of the priority list and that can go a long way in retaining and attracting loyal clientele. This article will go over some of the processes involved in getting certified and how you can prepare for your company’s SOC2 audit.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
SOC2 Audit
In order to receive a SOC2 certification, your company will need to undergo and pass a SOC2 audit. This is when a CPA (Certified Professional Accountant) analyzes your company’s security to assess whether it meets established SOC2 standards. This is done by following the SOC2 framework established by your company and determining how well your company complies when it comes to critical data.
Your auditor will begin by looking at a SOC2 controls list and analyzing how well each control is met and maintained by your business. This list is determined by the Trust Service Criteria (TSC) that your company is being audited for. Your company doesn’t need all five to get certified, only the Security criteria is required, but if other criteria are of high-value to your business, it is wise to run those through the audit as well. Many of the SOC2 requirement checklists above will help you determine this.
SOC compliance is not a catchall term. There are multiple variations of SOC and different types of audits for each variation. Most likely, your organization will need to follow SOC2 Type 2 requirements for audit involving customer data security. The SOC2 compliance Wikipedia page does a good job explaining the different levels and types of SOC compliances in general terms.
Utilizing a SO2 compliance checklist is a great way to prepare for an audit. They will most often follow the same, or very similar, SOC2 compliance requirements the auditor will be looking for to grant your company certification. Sticking as closely to the audit framework you create is the most foolproof way to do everything you can to prepare your business for the audit. Utilizing virtual chief information security officers like those offered by Trava Security will allow your organization the best chance of getting certified on the first audit.
SOC2 Audit Checklist
The value of using a SOC2 audit checklist to prepare can not be overstated. Just as you wouldn’t go into an exam with out preparing as best as you possibly could, a business should never go into an audit without first preparing as best it can. This article has covered the importance of using a SOC2 checklist to prepare your business, but what would that look like?
Some might build their own SOC2 compliance checklist XLS (Excel Spreadsheet) to better suit their needs, but there are templates available for download as well. Regardless of how thorough your SOC 2 compliance checklist template may seem, it is important to check that you have the necessary components before putting it to use. Here are some of the most important items to make sure your checklist includes.
- Determine your objectives. This refers to the framework mentioned above. Select the TSCs your business needs to be audited for the most. Again, security is required for certification but the other four criteria are not. Only include the criteria you absolutely need to to better your chances for certification. Audits are concerned with people, data management, risk policies, and software. Your job is to decide who and what will be considered during the audit.
- Evaluate your controls. You have your TSCs identified, now you need to look into how well you meet the standards set up for those criteria. In other words, what controls do you have in place to ensure that your customer data is protected? Defining your controls and ensuring they meet standards is a crucial step in preparing for your audit.
- Run a Readiness Assessment. This can be done internally if you know what you are doing. An external auditor can also be brought in to run a readiness assessment to make sure you don’t waste the money on an audit you weren’t fully prepared for.
- Close the gaps. After a readiness assessment will come the gap assessment. This will inform you on how far you are from meeting the standards of each trust criteria you are auditing for. Closing these gaps can be as easy as training employees on security protocols or as complicated as overhauling security controls and software. This step can take up to a few months depending on how far you have to go to close the gaps.
- Final assessment. Now that you’ve identified your security shortcomings, and closed the gaps they revealed, you need to make sure you didn’t overlook any important pieces. Running a final readiness assessment is exactly like the initial test above, only this one will determine whether you are ready for the real thing or not. If you’ve successfully closed all of your gaps, then you will be cleared to go for the audit. If you fail, you will have to likely run another gap assessment to see what fell through the cracks.
To reiterate, there are plenty of SOC2 compliance PDF downloads available to the public, but if they don’t involve all of these steps, then you might be led astray in thinking you are ready for certification.
Looking for a complete SOC2 Checklist? Trava has you covered!
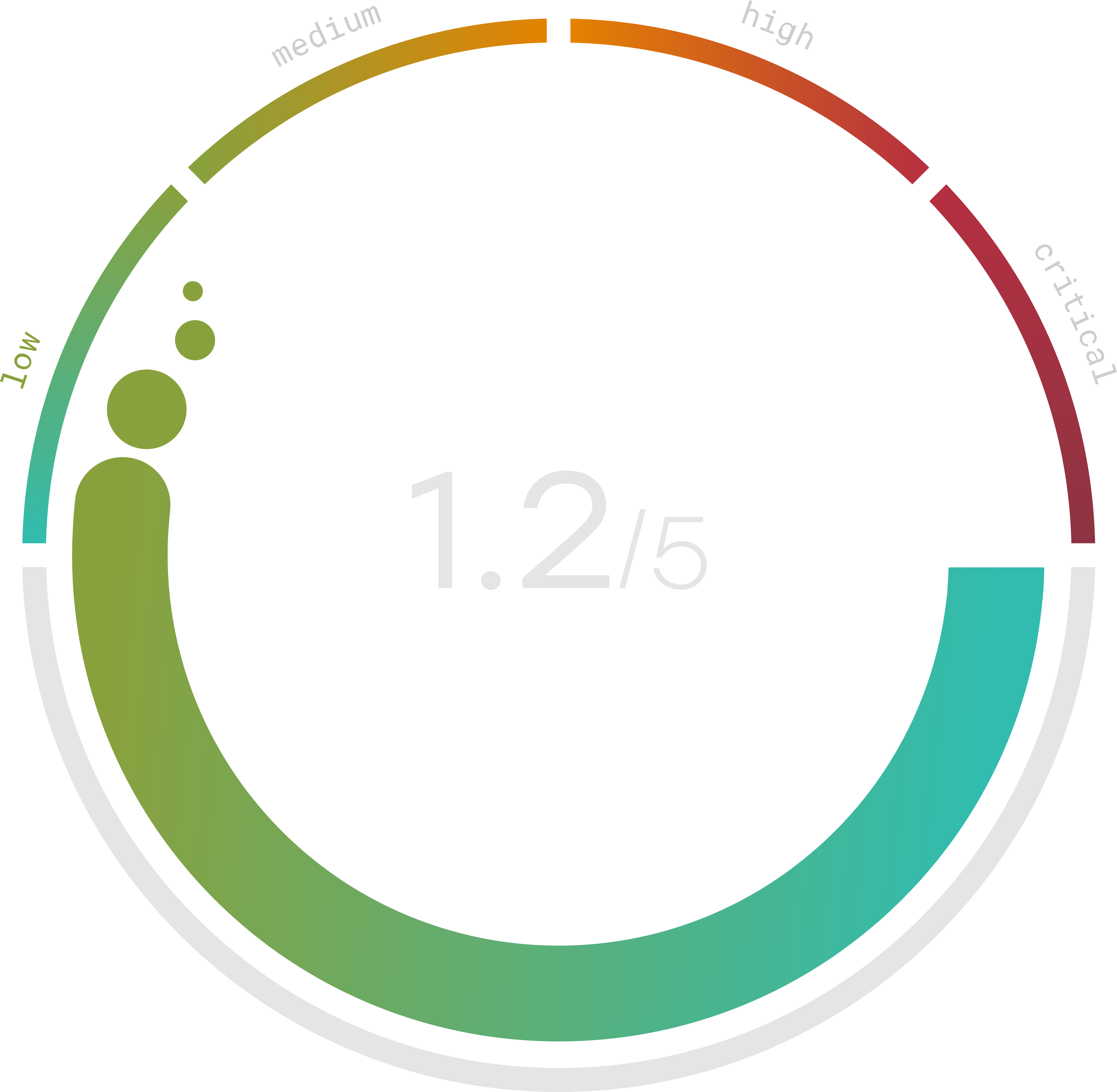
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
SOC2 Controls Checklist
There are quite a few SOC2 controls that an auditor will check. In the list above, there is information on how to prepare yourself for a SOC2 audit. You can use the list above as a sort of free SOC2 compliance checklist. The auditors themselves will be going through a SOC2 controls checklist to gauge your company’s ability to protect customer data. Specifically, a SOC2 type 2 controls list is likely what your company will be evaluated against.
Depending on how you analyze information best, you may be interested in a SOC2 compliance checklist excel download online, or a SOC2 guide PDF. it all comes down to how you can understand the information most effectively. Most likely, you won’t need to worry about getting your hands on a SOC1 compliance checklist PDF because of the different criteria evaluated. A more valuable download might be something like a SOC2 report example PDF. Again, remember which type of audit you are undergoing. A SOC2 type 1 report PDF won’t help you if you had a SOC2 type 2 audit.
To ensure your audit goes well, your management team will need to construct a SOC2 controls matrix to present to the auditor. Basically, this is a SOC2 controls list excel spreadsheet that outlines which controls you are currently employing. Taking a look at an online example of a SOC2 type 2 controls list excel sheet will give you a clear idea of what this needs to look like. Many audit firms will offer a SOC2 report review checklist to help you make sense of the audit report once the audit is complete.
AICPA SOC2 Controls List
The AICPA SOC2 controls list is something that changes, if ever so slightly, from year to year. It might be worth your time to have a download of a AICPA SOC2 guide PDF on hand for reference, but there are better ways to make sure you are prepared for everything.
For some of the assessments mentioned in the list above, A-Lign SOC2 assessments are great for making sure your security is up to the challenge. To help close any gaps you may end up having, Trava Security can fill that role for you. A variety of risk assessments and vulnerability scans can help you pinpoint where your company needs help and how to remedy the issues.
And a Trava vCISO (virtual Chief Information Security Officer) will guide you through the process. Learn more about how a Trava vCISO can help prepare you for SOC2 and security audits. Contact Trava today to find out how to keep your data secure.
