In today’s day and age, cybersecurity protection is essential for any group that uses digital systems to function. Without adequate protection, an organization can fall to the attacks of cyber risks.
Cybersecurity (definition being the measures taken to protect and prepare an organization from cyber risks) involves certain information security principles. If you look at a what is cybersecurity PDF, you may be able to see the various ways cybersecurity works and how you can strengthen your organization’s cybersecurity posture.
Cybersecurity comes in various forms and its details can depend on what industry you’re in, your particular risk factors, and if you have sensitive data that needs to be protected. The common types of cybersecurity include network security, cloud computing security, application security, Internet of Things (IoT) security, mobile security, endpoint security, and zero trust security. Each type of protection specializes in different cybersecurity challenges that your organization may face, and you may want to consider employing several of them to maximize your security.
Network security is typically meant to enforce safe web use policies within your organization. Many advanced network threat prevention technologies exist today. Network security software platforms may provide you with analytics and threat-hunting capabilities.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Cybersecurity
The Office of the National Cyber Director is the national cybersecurity center that was established in 2021. Homeland security recognizes the importance of cybersecurity, as it is often a matter of large-scale national security. Government agencies are constantly under attack by malicious cyber threats, whether it is data being stolen, propaganda being spread, networking systems being attacked, or another type of cybersecurity threat.
On the other hand, the question of how to prepare for cyber attack at home is a lot less complicated than how to protect a government organization from cyber attacks. One of the easiest ways to prevent your home’s systems and data from falling into the control of cyber attackers is to be aware of your vulnerabilities.
Essentially, you should think before you click. Is an email or text message looking a bit off? Don’t click any links attached to it. Next, are you using MFA for your important accounts so that they are more secure? MFA is an extra step you need to take when filling in a password. You may have to answer a question only you know, enter a PIN, or use a fingerprint ID. MFA is good for everything from social media accounts to gaming and streaming services, not just accounts like your bank and email.
Are all of your software updated to the latest version so that they are more readily able to withstand external attacks?
Another easy way to improve your security at home is to use strong passwords. Do not use common passwords like “password” or “123456”. Using names or birthdays is also dangerous. It is better to have a password of 16 characters, unique, and randomly generated. Password managers can help you generate a random password that takes hackers longer to crack, which also means that they are unlikely to try breaking into your account.
Cybersecurity Basics
Every U.S. cybersecurity agency is likely to have implemented the same cybersecurity basics. Take a look at any introduction cybersecurity PDF, and you will see similar cybersecurity notes related to cybersecurity best practices and a general cybersecurity framework.
The first thing to know about cybersecurity is why you need it. Large businesses, small companies, the government, and even individuals should be aware of the cybersecurity basics. Cybersecurity is essential for companies because of the potential losses you could face if there is a data breach, ransomware, or another type of successful cyber attack.
Companies face losing thousands, if not millions, of dollars because of cyber threats. They could even be forced to stop operations permanently. If data is breached, regulations may mandate you to notify involved parties, which means that you would take both a financial and reputational hit. It is absolutely possible for companies and careers to be ruined because of sinister cyber attacks. Luckily, there are good ways to improve your security.
Cybersecurity measures are far cheaper to implement. That is why every company should have a strong cybersecurity plan. It is typically a good idea to invest in employee cybersecurity awareness training, use multi-factor authentication (MFA), implement email virus detection software, and update to the latest security software.
Essentially all industries have seen a significant spike in cyber crime. The recent years of remote work mean that a lot of data and work has transitioned online, making cyber crime even more lucrative and dangerous.
Malware, phishing (social engineering) schemes, internal attacks, and hidden backdoor programs are just a few of the threats that have run rampant. Some of these types of threats can be more easily trained for, and awareness of them should be spread within your organization. For example, social engineering attackers often target businesses by sending an email and pretending to be a trustworthy source. They will include an attachment or a link that leads to data being breached, malware being downloaded, or another potentially costly result for your company.
At the end of the day, it is recommended that you mitigate your cybersecurity risks by taking steps to calculate your risk factors and strengthen your posture accordingly. As cyber crime evolves, cybersecurity software are also adapting to become more effective. If your company has a system for reporting and managing cybersecurity events, it can become easier to deal with threats as they come.
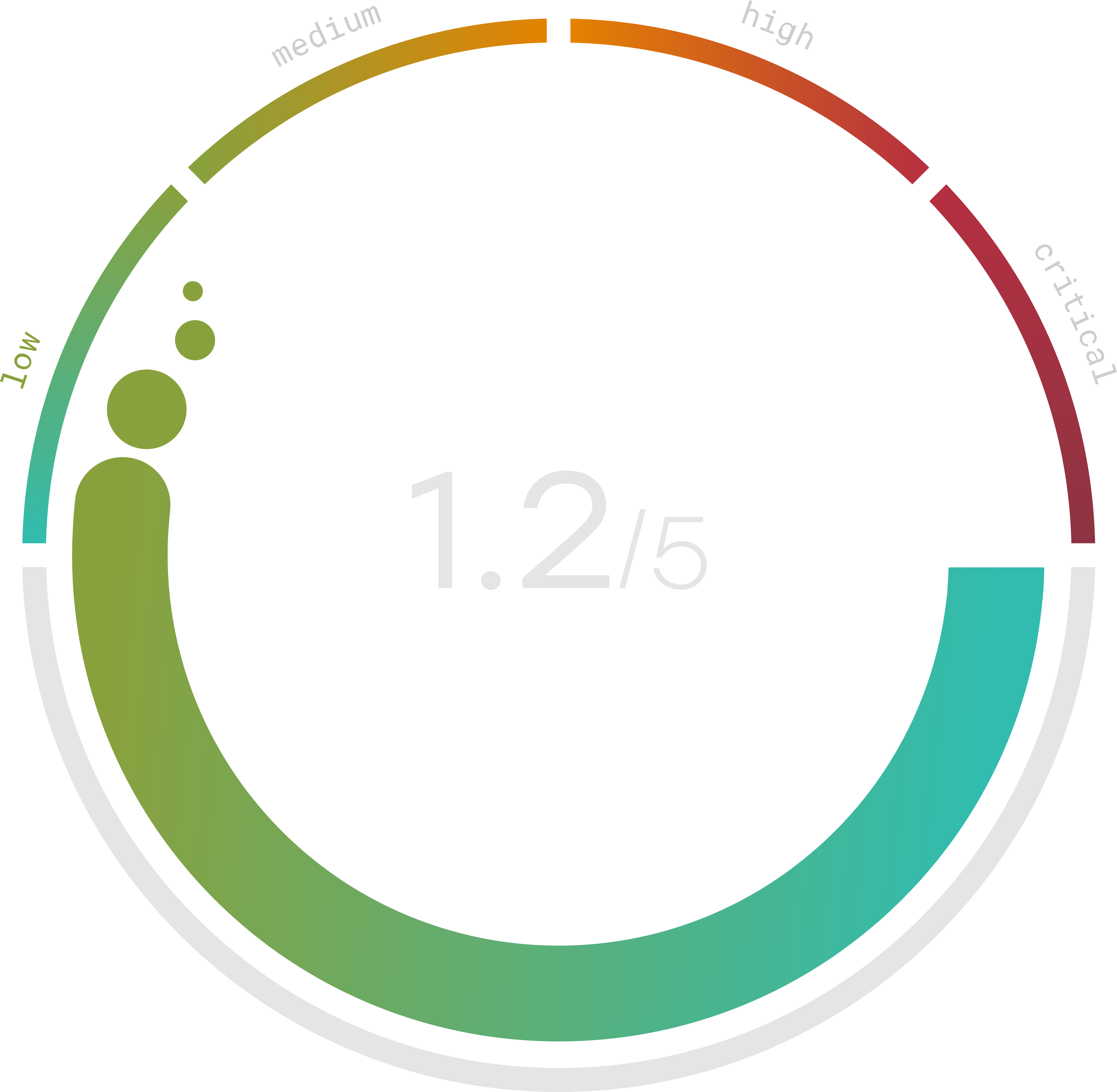
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Types Of Cybersecurity
Different cybersecurity categories exist to help your company become more resilient against the different types of cybersecurity threats. There are too many threats and unknown exploits to count and guard against, but the stronger your security posture, the more likely you are to recover without a program in case an attack does hit your organization.
Here are some cybersecurity examples and what they seek to protect:
- Information Security – Protects private, sensitive information of users from unauthorized access, identity theft, and other threats. User Authentication and Cryptography are common knowledge employed by information security professionals to protect their clients.
- Application Security – Protects software apps from risks. Vulnerabilities existing in an application’s design, development, installation, or upgrade phases can expose your company to dangerous cyber attacks targeting the app. It also helps keep your maintenance phase more secure.
- Network Security – Protects the usability and safety of everything related to a network, including shared data. Common examples include firewalls, Virtual Private Networks (VPNs), and antivirus software.
Other than the types of cybersecurity, you should also know the basic elements of a strong cybersecurity posture. You should identify what assets of your company need to be protected, such as sensitive customer information, trade secrets, and more. After that, you should make a risk management plan and alter your access permissions to properly manage threats.
Disaster recovery and business continuity measures are also necessary. At the same time, disaster recovery can be incredibly complicated. What contingency plans can you put in place to keep your organization’s infrastructure up and running? DDoS attacks and literal natural disasters can negatively impact your business, making you unable to access your servers and data. Fail-safes and backups can help prevent cyber attacks from completely wiping out your data and network.
As a crisis occurs, incident management is critical in keeping your company afloat and ready to react. What authorities do you need to contact, and what partners or employees need to know the details?
Finally, security education and awareness training can always able to improve the strength of your cybersecurity posture.
CISA
Established in 2018, the Cybersecurity and Infrastructure Security Agency (CISA) is the national cybersecurity center that leads the national cybersecurity protection system. It has comprehensive responsibilities and a robust national cybersecurity program to understand, manage, as well as reduce risk to the national cyber and physical infrastructure. It is an operational part of the Department of Homeland Security (DHS).
The difference between the CISA national cybersecurity policy and the Office of Management and Budget policy is that CISA mainly focuses on federal civilian government networks, as opposed to federal cybersecurity in general. Naturally, cybersecurity is critical to any nation’s safety and security. Critical infrastructure threats can pose huge risks to federal government networks and national security data.
CISA interacts with both public and private sectors to analyze, identify, and manage strategic risks. CISA understands that there are many cross-sector threats and needs and has decided to work with partners and collaborate with industry to build the necessary security posture for the nation. There are countless cyber, physical, technological, and natural challenges that CISA is constantly facing. More specifically, the four critical focuses of national risk management are Identify, Analyze, Prioritize, and Manage.
If you are familiar with the NIST Cybersecurity Framework, you may recognize some overlap between the CISA key focuses and the NIST Cybersecurity Framework.
