Cybersecurity is a part of risk management. Risk management is used to refer to the processes that are put in place to reduce a business’s exposure to potential harm.
Today, nearly every business relies on the internet in some way. For most companies, daily operations would grind to a halt if they did not have access to the internet. The internet allows people to work from almost anywhere in the world. At the same time, if a business is more accessible to employees, then it is also more accessible to criminals, hackers, and those who seek to take advantage of organizations for their own personal gain. This is why cybersecurity is so important.
Cybersecurity refers to the processes, practices, and technologies that a company uses to protect its programs, devices, and data from damage, attack, or access by unauthorized individuals. Often, people use the terms cybersecurity and information technology (IT) security in an interchangeable manner. During the past few years, technology has come a long way; however, so have hackers. As a result, cybersecurity is a continuously evolving process. For this reason, all businesses need to work hard to make sure that they stay up to date on the latest developments in this field. It is critical to stay ahead of criminals.
In this manner, cybersecurity risk management comes into play. There is a close relationship between cybersecurity and risk management because cybersecurity is a part of risk management. Risk management is used to refer to the processes that are put in place to reduce a business’s exposure to potential harm. When it comes to cybersecurity risk assessment, this means the risk to the company’s data, network, and devices. In this manner, enterprise cyber risk management is critical. When it comes to cyber risk management, all companies need to understand that this is an ongoing process and not a destination. There is no such thing as a business being totally secure. Instead, businesses need to continually assess where they stand and make sure they are doing everything they can to keep their data, and the data of their customers, safe from harm. This is where a cybersecurity risk assessment report developed using a cybersecurity risk assessment template is important. These steps can go a long way toward making sure that a business remains safe, secure, and ahead of the competition.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Cybersecurity Risk Management Jobs
Cybersecurity risk management is a field that is growing quickly. Because so many companies use the internet to handle even their most basic products and services, this is a field that is continuing to grow. As time goes on, companies depend more and more on the internet. As a result, cybersecurity risk management only becomes more important.
For this reason, cybersecurity risk management jobs are important as well. When it comes to cybersecurity risk management jobs, it is important to note that these positions come in many shapes and forms. Many people who work in the field of cybersecurity risk management have a degree, experience, or background in information technology. Often, those who work in cybersecurity risk management have just come directly from the IT department.
Because cybersecurity risk management is more important than ever, salaries are growing as well. A cybersecurity salary could easily start at $75,000 per year; however, this is a job that people rarely get straight out of school. Often, people who work in cybersecurity risk management get experience in the field first.
For those who have a position as a manager, a cybersecurity risk management salary could be above $100,000. This is comparable to the salary of an IT manager, who might be responsible for overseeing not only security but other issues related to the company’s technology processes as well. As people get more experience in the field of cybersecurity risk management, they should expect an information risk management salary to rise. As a result, jobs in cybersecurity risk management are incredibly desirable.
In addition to the pay, this is a position in which there is room for advancement. Those who do well in cybersecurity risk management could open up opportunities for themselves in the upper levels of information technology. This could include promotions to executive levels for those who are interested in the financial side of IT as well. This is just another reason why cybersecurity risk management is a growing field.
Cybersecurity Risk Management Certification
Because jobs in cybersecurity risk management are so desirable, there are lots of people who are looking for ways to increase their competitiveness on job applications. One possibility is to earn a cybersecurity risk management certification. Those who take the time to earn this certification show potential employers that they have put in the hard work, undergone the cybersecurity risk management training, and are prepared for the challenges that come with a job in this field. With this in mind, there are a few options from which to choose when it comes to cybersecurity risk management training and certification programs.
One of the most popular is a certification called the CRISC certification. This stands for Certified in Risk and Information Systems Control. CRISC certification training prepares potential IT risk managers to deal with the latest threats in the field. This certification is a demonstration of expertise when it comes to identifying and managing risk in the IT field at the enterprise level. Furthermore, this certification shows employers that individuals have the proper training in implementing and maintaining controls in information systems.
There is another cybersecurity policy certification in which IT professionals might be interested. This is the Certified Cloud Risk Management Professional, or CCRMP certification. This is a certification that signifies a certain level of expertise when it comes to cloud computing. The cloud is a rapidly growing space in the business world. Countless companies now use the cloud to store and distribute information; therefore, this certification is also incredibly popular among those who work in cybersecurity risk management.
Finally, those looking to start or further a career in cybersecurity risk management might also want to earn a CISSP certification, which stands for Certified Information Systems Security Professional certification. This is a popular security certification for security analysts. There are some professionals in cybersecurity risk management with multiple certifications.
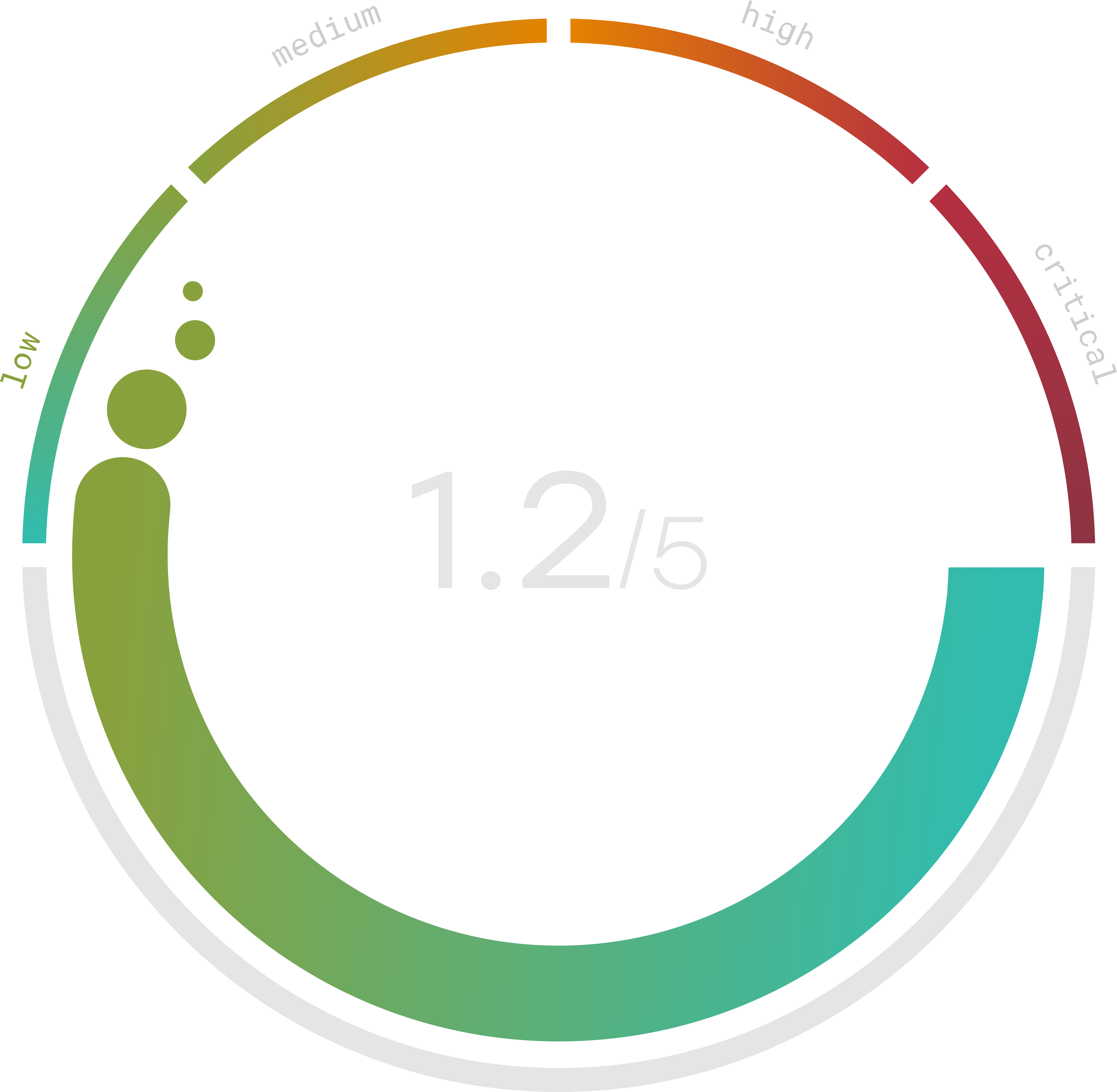
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Cybersecurity Risk Management Frameworks
When it comes to cybersecurity risk management, it is always a good idea to approach this process with a strong framework. A framework is a template by which trained professionals can come up with a strong risk management policy. One popular method is the NIST risk management framework. This cybersecurity framework is used to guide cybersecurity risk management professionals as they come up with strategies to protect the company. The NIST cybersecurity framework is a model that focuses on continuous improvement and compliance. The NIST cybersecurity risk management framework steps include:
- Categorize the System
- Select the Controls
- Implement the Controls
- Assess the Controls
- Authorize the System
- Monitor the System
This cybersecurity framework template is one that focuses on making risk-informed decisions in a continuous manner. Using this method, the goal of this cybersecurity risk assessment framework is to make sure the system is as secure as possible.
While there are multiple ways to approach cybersecurity risk management, the NIST cybersecurity framework spreadsheet is a strong starting point. Some of the major advantages of this type of cybersecurity risk management framework include:
- Cybersecurity risk management operates in an unbiased manner
- This cyber risk management framework is set up for long-term success
- Using this cybersecurity risk management framework, there are ripple effects throughout the entire company in a positive manner
- The framework is adaptable and flexible
For these reasons, everyone needs to think carefully about how they want to approach cybersecurity risk management.
Cyber Risk Assessment Tools
When it comes to risk management strategies in cybersecurity, it is important to leverage the most advanced tools on the market. A strong cybersecurity risk management program is going to combine training and expertise with the right cybersecurity risk assessment tools. One of the most important cybersecurity risk assessment tools is a straightforward cybersecurity risk assessment checklist. A checklist for cybersecurity risk assessment should include:
- How well is the context understood? This should include threats, risks, supply chains, regulatory controls, and governance.
- How well are the assets protected? This should include asset awareness, data security protocols, information storage, maintenance schedules, and IT management.
- How well are any anomalies detected? This should include analysis, monitoring, and notifications.
- How is the response handled? This should include controlling responses, coordinating responses, mitigating damage, and evaluating the quality of these responses.
- How well is the recovery process managed? This should include controlling the recovery, coordinating the recovery, and the completeness of the recovery.
The answers to these questions should be included in a cybersecurity risk assessment report. Then, they could even be plotted in a cybersecurity risk assessment matrix. Over time, companies can use cybersecurity risk assessment tools to monitor trends, look for threats, and make sure that any and all issues are addressed in an appropriate manner. Remember that the goal of a cybersecurity risk assessment is to make sure the company is ready to respond to threats that might take place in the digital world. The better companies leverage the data collected in a cybersecurity risk assessment, the better they will be able to protect not only their data but that of their customers and business partners as well.
