Good risk management strategies are ongoing processes to pinpoint risks, analyze the impact, and provide solutions to offset risks.
Every year, businesses collectively lose billions due to cybercrime. No company is safe, not even small and medium-sized businesses. Threat actors are specifically targeting SMBs because they assume these companies are easy targets with small security budgets and are unable to afford a robust IT staff. Some estimates suggest cybercrime will cost the world $10.5 trillion per year by 2025.
Cybersecurity assessment tools are a vital part of safeguarding an organization’s electronic assets and equipment. To better understand and view a cybersecurity risk assessment report sample, the National Institute of Standards and Technology (NIST) has published a detailed PDF that explains the overall concept, along with specific examples of the different sections associated with performing a formal cyber risk assessment. However, in our article, we have simplified the concept and have broken it down into sections.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Cyber Risk Assessment
Unless you’ve been actively involved in cybersecurity processes, you might not be familiar with a cyber risk assessment. Essentially, a cyber risk assessment, as defined by the NIST, is used to identify, estimate, and prioritize an organization’s risk relating to operations, assets, individuals, and other organizations to consider when they use or operate information systems.
The cyber risk assessment’s primary purpose is to keep stakeholders up-to-date and to provide information on the impact of a data breach, the likelihood of certain events occurring, what technology and human vulnerabilities exist, and what your company’s comfort level is when it comes to risk. Once the full assessment has been completed, the components will be brought together to create a formal report. This document helps decision-makers form both proactive and reactive plans for dealing with cybersecurity preventatives, along with a better understanding of the different types of events and the appropriate responses to them.
After you’ve determined the largest threats to your company, plans can go forward to integrate protective cybersecurity measures to safeguard your business against both identified and unidentified risks.
Cybersecurity Assessment Template
Businesses just starting the journey to achieve stronger cybersecurity practices in their organizations aren’t likely sure where to start. Much like templates for other processes, a cybersecurity assessment template can help both simplify and streamline this task. NIST has established the CIS Critical Security Controls, which businesses and other organizations can utilize to gain insight into best practices that can be integrated into cybersecurity plans to address the largest and most common vulnerabilities.
NIST’s Cybersecurity Framework also helps simplify the risk assessment process, along with providing insight into common governance issues businesses must address. Most businesses find NIST, along with other privately designed cybersecurity assessment templates, to help the process become more straightforward.
Understanding the risks helps you identify any flaws, vulnerabilities, or other absences in your cybersecurity procedures. After any problems have been pinpointed, you can learn how to strengthen weaknesses associated with your data and IT assets and determine the steps to take to remediate any issues.
Cybersecurity Risk Assessment Software
Businesses face many different types of cyber risks. Some of the most common cyber threats include malware, data leaks, phishing, ransomware, human errors, insider threats, and other types of cyberattacks. Cybersecurity risk assessment software tools can help you determine vulnerabilities, rank them, and ascertain the negative impact if a threat actor succeeds in their attack against your company. Essentially, digital tools can help you calculate risk. This will assist you in ranking the most probable to least probable, helping decision-makers determine where cybersecurity resources should be prioritized.
Cybersecurity Assessment Questions
In addition to using digital tools to help identify and calculate risks, going back to basics can also significantly help you. As a part of performing your risk assessment, you’ll want to ask yourself several cybersecurity assessment questions. Important areas to think about include questions associated with human risk factors. For instance, your company’s level of employee knowledge of cybersecurity and training, how vendors and other third parties practice cybersecurity, and what information or other assets threat actors target. Essentially, pinpoint questions related to human risks and external threats that exist.
Another set of cybersecurity assessment questions should focus on how your company views and responds to cybersecurity. For instance, ask yourself what security protocols are in practice, is there a formal written plan, how much emphasis you put on compliance. Compliance, while important, often provides a false sense of security. Also, determine who is in charge of the plan and will address identified vulnerabilities. Finally, ask yourself how your company responds to breaches and other security events and what level of risk you are willing to accept.
Asking questions related to both internal and external threats is critical to your overall cybersecurity risk assessment process.
NIST Cybersecurity Assessment Tool
NIST is known in the cybersecurity industry as the “gold standard” for the processes and steps associated with risk assessment. Incorporating NIST cybersecurity assessment tool concepts can go a long way towards strengthening cybersecurity procedures, not to mention avoiding suffering hefty financial losses, damage to brand reputation, and lengthy service outages.
NIST Risk Assessment Example
NIST uses five domains in its security framework. Businesses following the NIST risk assessment example will often use the five domains included in their security framework. These “pillars” are as follows:
- Identify
- Protect
- Detect
- Respond
- Recover
Used collectively, these five functions work concurrently and consistently. Together, they form a solid foundation for businesses to build upon and create a strong cybersecurity risk management process.
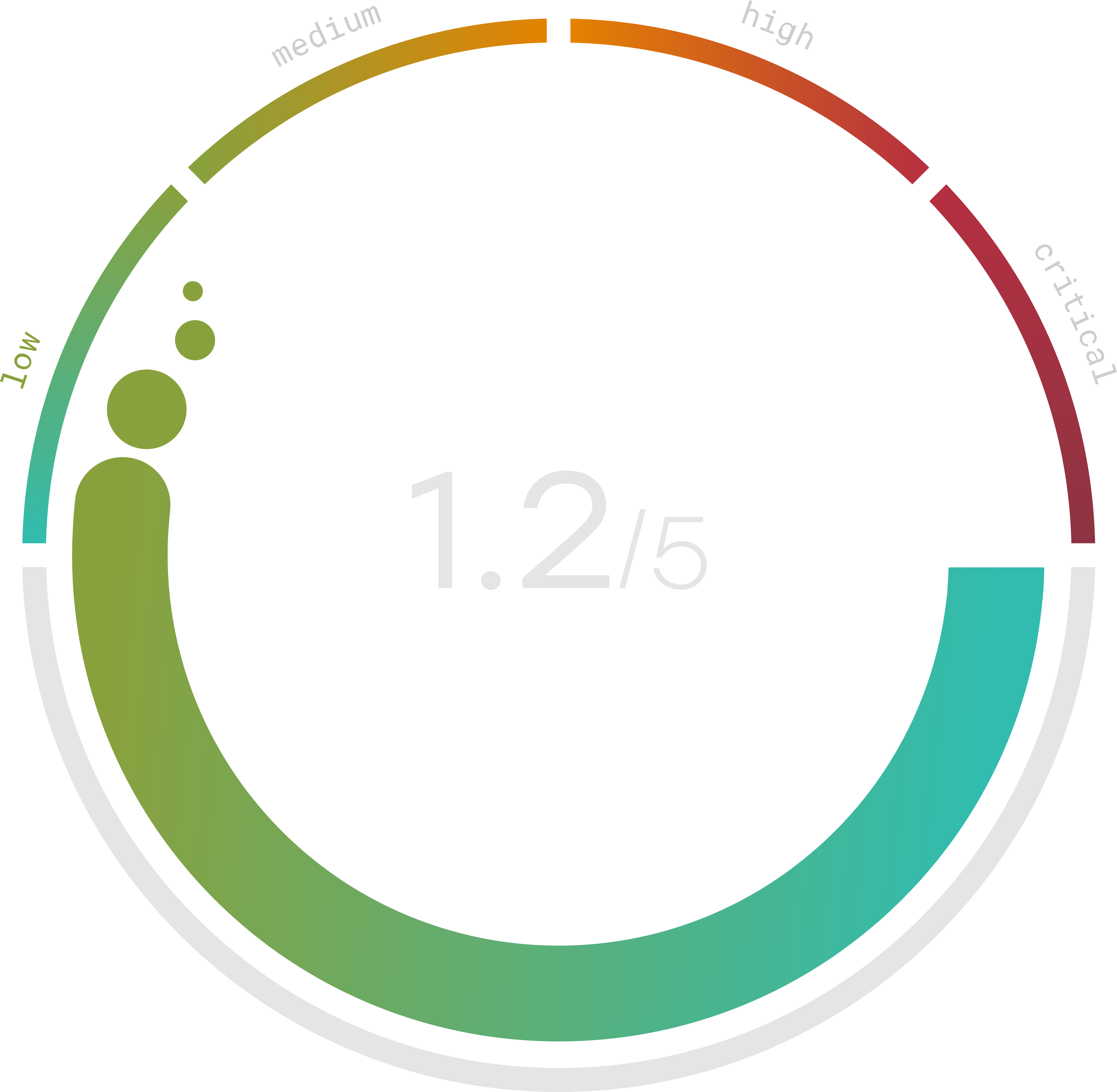
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Microsoft Cybersecurity Assessment Tool
The Microsoft Cybersecurity Assessment Tool helps you create a cybersecurity action plan based on the facts. It’s challenging to have to sort through different documents and files to find everything linked to your cybersecurity risk assessment plan and your cybersecurity protocols. CSAT (Cyber Security Assessment Tool), created by QS Solutions on the Microsoft platform, makes it easy for businesses to integrate it using existing technology. This automated software also uses a questionnaire (based on CIS framework) to collect data related to security policies and other important key indicators.
Trava offers an automated cybersecurity assessment tool that checks for vulnerabilities in external and internal environments with a number of scan types. Users may schedule and manage assessments from one convenient platform, streamline results with simple, aggregated reports, and prioritize mitigation action plans to help bolster cybersecurity. Decision-makers can then decide the best course of action and determine where resources should be allocated. All helping to ensure a company’s level of compliance.
Cybersecurity Maturity Assessment Excel
Many businesses often think it’s a good idea to use everyday digital tools, such as Excel and email, to track data, company cybersecurity policies, and other sensitive information. What they don’t realize is that using these tools as an assessment can put their companies at risk for non-compliance with regulatory guidelines or laws. It can also lead to significant oversights which can put companies at increased risk of cyber threats.
Using professional-level tools that are properly vetted and meet security standards better positions your company and decreases the likelihood of important factors being overlooked, especially as regulations and threats change. Not to mention, these tools can also save time, require less manpower, and are, overall, more cost-efficient.
Risk management is not a one-and-done task. Good risk management is an ongoing process that continuously pinpoints risks, analyzes the impact, and provides solutions to offset risks.
Source
- https://www.upguard.com/blog/cyber-security-risk-assessment
- https://csrc.nist.gov/glossary/term/assessment
- https://www.bitsight.com/blog/information-security-risk-assessment-templates
- https://www.sans.org/blog/cis-controls-v8/
- https://azuremarketplace.microsoft.com/en-us/marketplace/apps/qs-solutions.cyber-security-assesment-tool?tab=overview
- https://cybersecurityassessmenttool.com/microsoft-assessments/
- https://www.scasecurity.com/nist-security-framework/
- https://cybersecurityassessmenttool.com/#:~:text=The%20Cyber%20Security%20Assessment%20Tool%20(CSAT)%20is%20a%20software%20product,recommend%20improvements%20based%20on%20facts.
- https://www.entrepreneur.com/article/364015
- https://cybersecurityventures.com/hackerpocalypse-cybercrime-report-2016/
- https://www.investopedia.com/financial-edge/0112/3-ways-cyber-crime-impacts-business.aspx
