IT risk assessments are essential for businesses because they help minimize the fallout from cyber attacks.
The assessments are increasingly replacing checkbox compliance as an effective cybersecurity program for many organizations. Today, many companies are taking a greater interest in risk assessment for managing their security postures.
Information security risk assessment tools are used to determine the severity of risks in an organization and how to deal with them. They act as regulatory frameworks that help organizations to build risk-based cybersecurity programs. When choosing a cybersecurity risk assessment template, the most crucial factors to consider are alignment and utility. You have to ensure that the risk teams align with compliance teams to ensure risk and data security teams collect accurate information for decision making.
Cybersecurity risk assessment templates are the most effective approach to a risk management strategy. It is a baseline method and a means to track risk mitigation guides toward security strategy. Businesses are shifting from compliance-based to risk-focused cybersecurity program management due to the need for a more tailored approach to address cybersecurity risks specific to the organization. A compliance-based system does not provide a customized way of assessing risk in an organization. Hence, businesses with frameworks already in place can use cybersecurity assessment tools as guidance to assess the cybersecurity risk within a company.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
NIST Cybersecurity Risk Assessment Template
Information security risk assessment templates are replacing checkbox compliance as an effective cybersecurity program. When it comes to improving cybersecurity in your organization, one of the crucial things to do is carry out a cybersecurity risk assessment. The network risk assessment template is offered by third-party consultants to reveal risk insights and how to deal with them. There are several security risk assessment guides and templates that you can use.
Risk can be determined using a variety of tools. One popular guide is the NIST SP 800-30 as a recommended security control for federal information systems. According to the NIST template, vulnerability analysis encompasses areas of management, operational, and technical controls. Management controls deal with managing any risks on the system. Operational control deals with the operating procedures performed to an information system, while technical control entails hardware and software protection measures.
The NIST Cybersecurity Framework is a guideline for conducting a risk assessment by the National Institute of Standards and Technology. NIST has outlined its guidelines for conducting a cybersecurity risk assessment for different organizations. Businesses of different sizes have widely applied NIST guidance in their organizations due to its popularity. This is because the NIST Cybersecurity Framework recommends the SP 800-30 as one risk assessment methodology available to conduct a risk assessment on IT networks.
The NIST risk assessment template uses a hierarchical model that makes it suitable for most organizations. The value of using the NIST risk assessment checklist is a large supporting body of work that comes with the template. In essence, there is a robust ecosystem comprising guidance and other supporting documentation that NIST provides to guide businesses regarding cybersecurity risk assessment. This guidance, as provided by NIST, has been applied across organizations of all industries.
Cybersecurity Risk Assessment Tools
There are several cybersecurity risk assessment tools you can use to uncover cyber risks. These assessments are offered by third-party consultants to reveal risk insights into your system. The cybersecurity risk assessment report sample facilitates monitoring, testing, dashboards, and reports on the state of a network. They can be used to provide continuous risk insights. These are some of the software tools that you can use to perform a cybersecurity risk assessment.
Vendor-provided tools are one type of application security risk assessment used to determine an organization’s inherent risk profile. The vendors that offer different components of your IT environment often provide tools to scan their products for vulnerabilities. For example, Microsoft’s security compliance toolkit can be downloaded and used to review operating systems and applications. Vendor tools are sometimes available at no cost, offered as part of a broader cybersecurity assessment by their providers.
Breach- and attack-simulation tools are also used in risk assessment to test for network vulnerability. These cybersecurity risk assessment matrices involve an agent trying to penetrate your system under controlled conditions to assess security measures and identify any vulnerabilities. Many organizations depend on third parties to provide penetration tests and insight into network security. These breach- and attack-simulation tools will test your system using automated means informed by the latest threat intelligence. They are a good means to provide insight and understanding of cybersecurity risk.
Security rating tools are used to measure the quality of information security initiatives in an organization. These devices offer instant insights into the attack surface of an organization. The ratings are derived from verifiable and objective information. Businesses can use security ratings to determine how secure their vendors are at a glance. Recently, organizations have used security ratings to get insights into compromised systems and other cyber diligence factors.
There are also automated information security risk assessment questionnaires that are used to verify that appropriate information security practices are followed. These questionnaires can help businesses improve coverage. They can act as vulnerability assessment platforms used to identify security concerns.
Cybersecurity Audit Checklist
A cybersecurity audit checklist comprises numerous items that come together for a complete risk assessment. The cybersecurity infrastructure determines how well your network and data are safeguarded from threats and outside attacks. Developing a cybersecurity audit checklist gives companies a way to quantify their resources and learn about their networks’ vulnerabilities. The information can be used to map out appropriate solutions.
Some of the security risk assessment steps that cover cybersecurity threats include antivirus updates since having an antivirus application may not be enough to protect sensitive information. Instead, you have to regularly update your antivirus with details on the newest viruses and other malware.
Second, the cybersecurity checklist should include a firm password policy with multi-factor authentication. The IT policy should also mandate complex passwords and make sure all passwords are changed to increase security.
You should also implement device security on your IT security audit checklist that establishes a strong policy regarding the use of personal devices for work. Any device that contains client data and sensitive information should be secured both physically and digitally to protect the information.
Data encryption should also be part of the cybersecurity audit checklist. Firms should ensure they encrypt any data that leaves the office and regularly review backup logins. They should also restore files randomly to ensure they will work when needed.
The checklist should also include keeping the operating systems updated. Employees should be reminded to set the operating systems for automatic updates to protect against malware and virus infection.
At the same time, the information security compliance checklist should entail minimizing administrator privileges to protect the devices from attack. Allowing free access to workstations exposes the machines and other tools to security threats that can affect the entire network.
In essence, a cybersecurity audit checklist is an assessment tool that allows businesses to understand their current resources and deficits. Information security risk assessment templates should guide enterprises toward a more secure future. The audit checklist comprises actions taken to assess the risks, identify security threats, and reduce vulnerabilities.
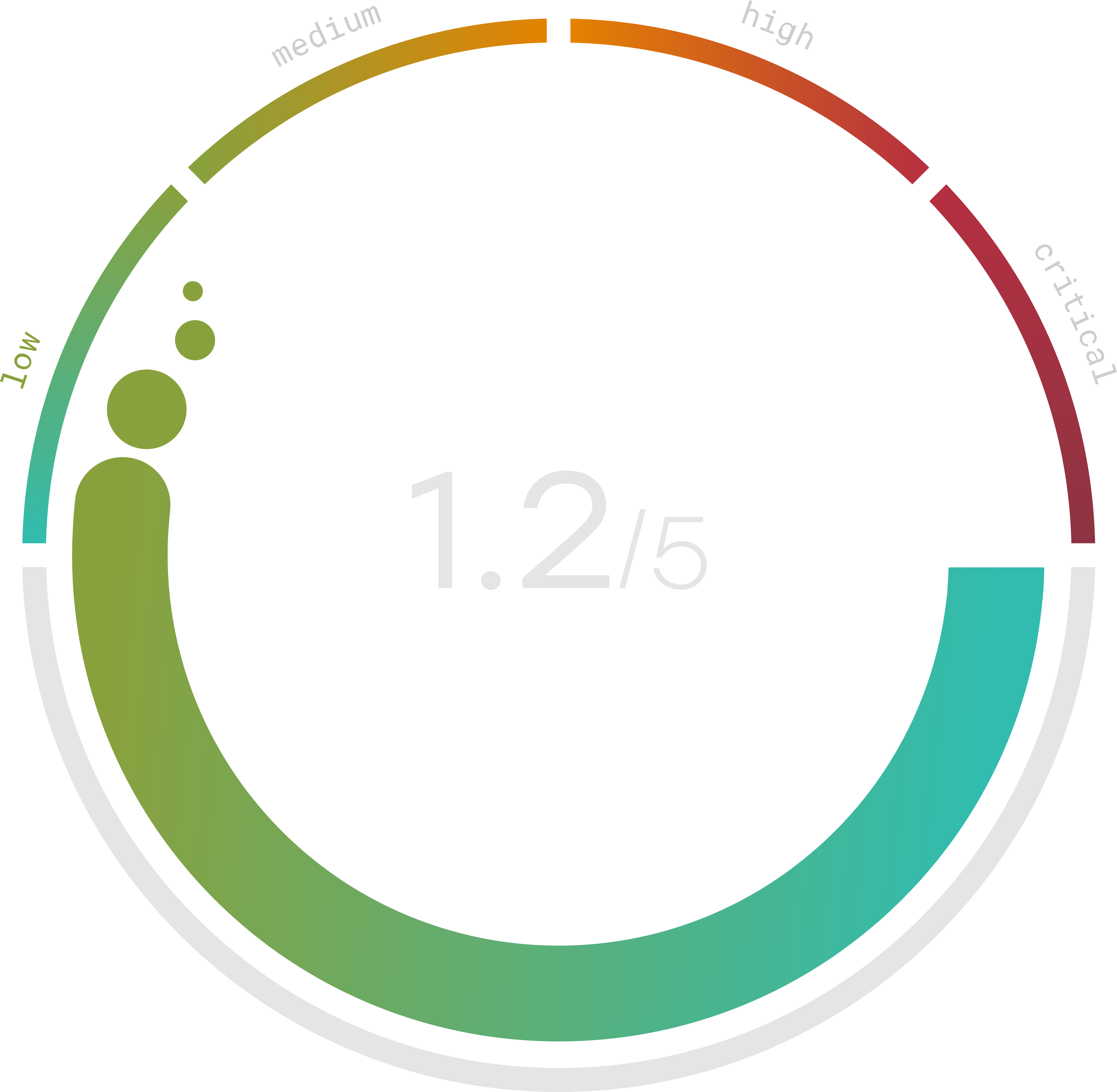
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Risk Assessment Report Template
Today’s network and data security environment is complex and diverse, demanding risk assessment to deal with any threats. The risk assessment scope entails evaluating risks to a system and determining any looming threats. The risk assessment report template conveys all the information and risk factors to top management for efficient decision making.
Risk factors play an essential role in influencing the success of planning and organizing. Organizations use this information in a report for cyber risk management, where they make decisions and provide solutions that will protect a system from attacks. An audit report is crucial for any company in conveying all data regarding revenues, payments, and any financial transactions.
A vulnerability assessment report template is an essential tool for IT managers to use when determining the potential harm to a security system. The cybersecurity assessment report provides businesses with the ability to provide security protection and meet the regulatory requirements for system security. It documents risk assessment activities to help an organization understand risks to a system.
The cybersecurity risk assessment report template provides an assessment of how well a security system is prepared for attacks. The risk assessment report will identify threats to a network and evaluate any loopholes in the system that can be exploited. Furthermore, the security assessment report template analyzes any potential impact of the threats to an organization.
IT Risk Assessment Questionnaire
Risk assessment describes how to identify and evaluate threats with the potential to cause harm. Risk assessment questionnaires help perform this function. An IT risk assessment questionnaire is designed to help businesses review and document their information processing activities’ risk profile. It helps organizations understand their systems’ security postures and determine whether they are doing enough to secure their networks.
The primary focus of a security assessment questionnaire includes security policy assessment, human resource security, asset management, communication, operational management, and physical and environmental protection. Simultaneously, an IT risk assessment questionnaire deals with business continuity and compliance with all protocols.
The sample questions in an information technology risk assessment questionnaire include whether an information security policy and security strategy exist in an organization. You should also use the application risk assessment questionnaire to describe the lifecycle process of information security policies at your organization. Another question is whether appropriate parties were involved in developing systems and how the policies were communicated.
In essence, adequate IT risk assessment helps promote awareness of possible risks and manage them. It is broken down into identifying threats, developing system diagrams, filling out controls, and creating an action plan to mitigate cybersecurity risks. You can then conclude the overall sufficiency of risk assessment with an evaluation of the problem.
The information security questionnaire for vendors is a tool that includes risk assessment questions for IT management. The questions assess risks in IT strategic management, IT processes, management aims and directions, performance evaluation, and IT risks.
