The rise of the internet has led to the creation of numerous databases containing sensitive information about individuals. These include credit card numbers, bank account details, home addresses, and other private information. When a company has to handle this type of information, it’s important to understand the position each of its employees holds with it. A security policy protects your business from legal issues. If you do not have a security policy in place, your business could face penalties if they find out that you did something illegal. You may get fined or lose your license if you violate any laws regarding privacy or hacking.
A cybersecurity policy should outline what your company’s position is towards cyber-attacks, including how they are going to respond to any incidents that occur. This document should include details about what information is stored where, who has access to this information, what controls are put in place to protect these systems, and what steps are taken to detect any vulnerabilities that might exist.
The first step in establishing any IT security policy is to define what it means. An IT security policy template should describe how your organization expects its systems to function and how they are expected to behave. This includes defining acceptable use policies, procedures, and standards for access control, data storage, encryption, identity management, etc. An IT security policy template should include information about who has access to what systems, what they need to do to get access, and how long they have access. You’ll want to include this information in your policies for both your network and endpoint devices, including laptops, tablets, smartphones, etc.
The National Institute of Standards and Technology (NIST) provides many helpful cybersecurity policies that can be used as a reference. These policies are divided into three categories: general, network, and physical. General policies cover areas like data classification, encryption, and privacy. Network policies deal with issues like intrusion detection and prevention, firewalls, and authentication protocols. Physical policies cover topics like disaster recovery and storage management. NIST policy templates have developed a cybersecurity framework to help organizations assess their current state, identify gaps, and create a plan for improvement. According to Sans, a cybersecurity policy can include anti-virus guidelines, a data breach response policy, and an acceptable use policy. Security policy templates consist of various components.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Cybersecurity Policy
Cybersecurity Policy is the document that outlines the company’s overall strategy toward cybersecurity. This includes any and all threats to the company’s network and data, as well as how they are going to prevent them from happening. A good cybersecurity policy should include not only what steps need to be taken but also who needs to take those actions.
A cybersecurity policy should clearly define what your organization stands for and how it intends to protect its assets from potential threats. This policy should outline the general principles that govern your company’s approach to cybersecurity. In addition, this policy should include specific guidelines regarding the responsibilities of employees and management, as well as any procedures for handling incidents. The University of Wollongong Australia provides an excellent cybersecurity policy example PDF. This cybersecurity policy PDF provides a neat layout such as policy responsibilities, the purpose of the policy, policy principles, and history changes. A list of information security policies is important to ensure all employees know exactly what they can do to keep their personal information private and secure. In addition, this will help your organization avoid any future liability if someone does manage to steal sensitive information.
Having a cybersecurity policy can help companies avoid costly data breaches. Companies that have a clear understanding of their vulnerabilities can proactively take measures to mitigate those risks. They can also use this knowledge to determine whether they need to invest in additional tools and resources to secure their networks. In order to create a successful cybersecurity policy, organizations first need to understand the business risk associated with cyberattacks. This requires a thorough assessment of the organization’s current security posture. Once the organization has identified potential weaknesses, it should then develop a strategy to address these issues.
Importance of Security Policy
Security policies are a set of rules that govern the access control system used to protect information assets. They define who has access to what data, how they can use it, and when they should no longer have access. A security policy is a collection of statements about the organization’s needs and desires for its network environment. It is the foundation upon which an effective security architecture is built on.
An information security policy framework is the best way to provide protection against hackers. It helps you to protect your business from different types of cyber threats. A company security policy PDF should be created so that a template is created for future policies going forward. This document provides much useful information about how you can protect your business from hackers. They can help your organization to achieve its goals and objectives in an organized fashion. Security policies should be developed based on the business needs, risk assessment, and legal requirements. When you develop security policies, make sure that they are well-written and easy to understand. You need to ensure that the security policies are implemented correctly. If not, then they may create unnecessary problems for your organization such as miscommunication and error.
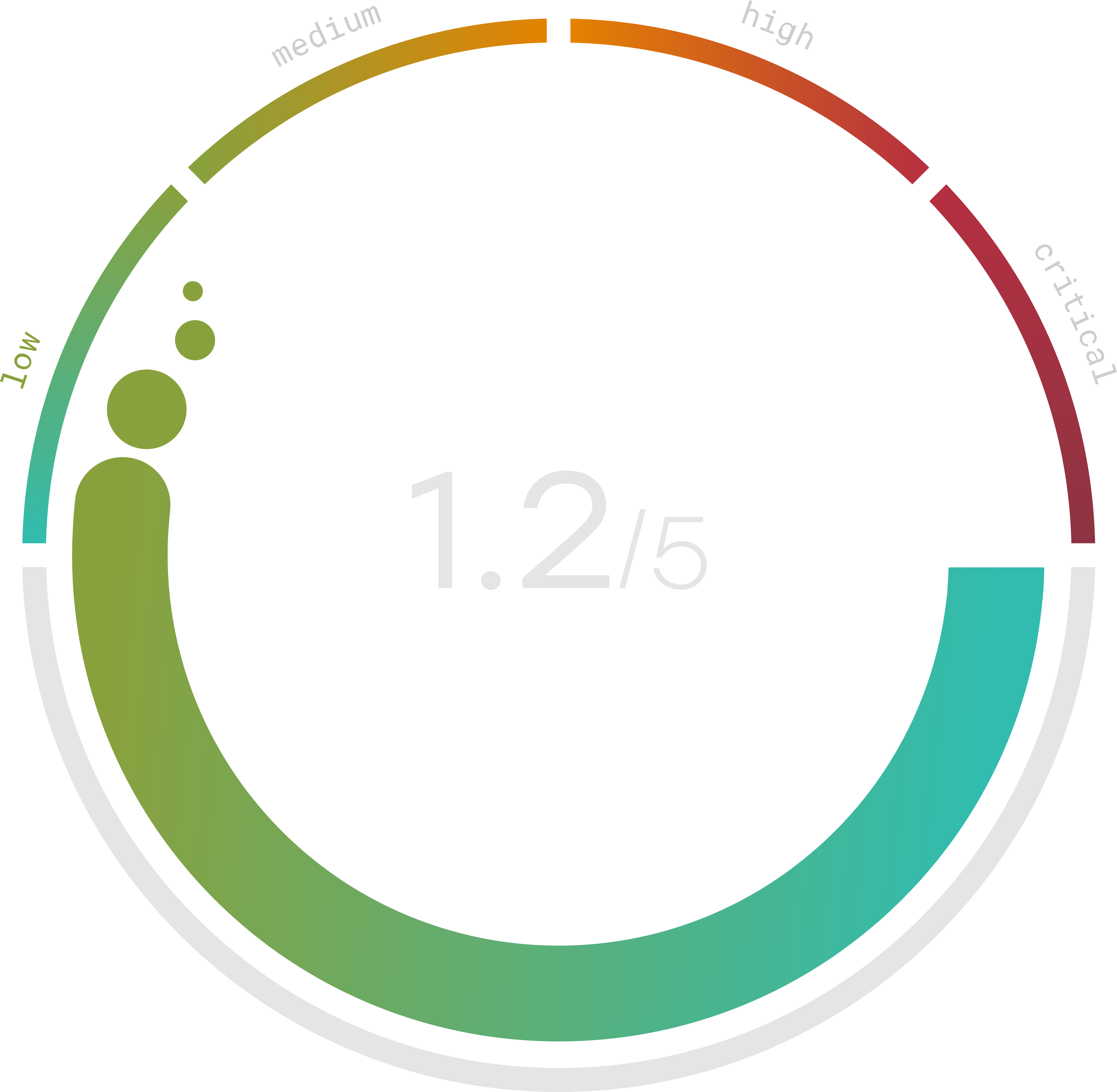
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Cybersecurity Policy For Small Business
All cybersecurity policies for small business should set up a cybersecurity policy template for their organization. Whether your business is an online or physical setting, it’s important to set cybersecurity policies. You should have a written document that outlines these rules. This way, if someone does something wrong, they know exactly what they did wrong and how they can correct their mistake. In addition, you want to make sure that everyone knows what they are expected to do. If you don’t have a formal security policy, you could end up being sued. When creating a cybersecurity policy template for small business, consider checking out this sample information security policy for small business below.
The first step towards any successful cybersecurity program is developing a comprehensive cybersecurity policy. A well-written cybersecurity policy should include the following elements:
- A statement that defines your organization’s mission, vision, values, and goals.
- An overview of the types of threats that could impact your organization.
- A description of how your organization plans to protect its assets from these threats.
- A list of the responsibilities of each employee in relation to protecting the organization’s assets
Don’t risk and afford to wait until a breach happens. The cost of a breach can be high, and you don’t want to pay out those costs. There are many ways hackers could gain access to your systems and cause damage. Your competitors are investing heavily in their own cybersecurity programs, which only will help you both compete in the long run. Having cybersecurity policies is important since employees may be tempted to steal information from your system.
Company Security Policy Example
When a company establishes a company security policy example, they are providing a summary of its policies concerning the protection of information systems and data. The data security policy template provides an overview of the Company’s information technology (IT) security program and describes how a company ensures that IT resources are protected from unauthorized access, use, disclosure, modification, or destruction.
If your business has any type of data that can be used to identify you, then it needs to have some sort of security policy in place. This way, if someone were to get their hands on this information, they would not know who you are. You want to make sure that all employees are aware of what they should do if they find out about this kind of information. If something like this happens, then it could lead to legal issues for your company.
A company should recognize that the protection of personal information is critical to its business success. It’s important to adapt to a comprehensive approach to managing the risks associated with the collection, use, and disposal of sensitive personal information. A possible cybersecurity policy sample can include the implementation of appropriate physical, administrative, technical, and organizational controls to safeguard the privacy and confidentiality of personal information. Creating security policy examples PDF and information security policy PDF ensures that security policies are clear and organized neatly for your company.
A source that can you review the strength and organization of your cybersecurity policies is Trava Security. Trava Security offers options to help your company increase revenue and prioritize cyber risk management and business protection. Trava Security also finds ways to keep you protected with helpful insights and solutions. Our professionals will work with you to create a professional and safe cybersecurity policy for you at a great quote. Sign up today if you are interested in working with us!
